Breadcrumb
Feedback-based access schemes in CR networks: A reinforcement learning approach
In this paper, we propose a Reinforcement Learning-based MAC layer protocol for cognitive radio networks, based on exploiting the feedback of the Primary User (PU). Our proposed model relies on two pillars, namely an infinite-state Partially Observable Markov Decision Process (POMDP) to model the system dynamics besides a queuing-theoretic model for the PU queue, where the states represent whether a packet is delivered or not from the PU's queue and the PU channel state. Based on the stability constraint for the primary user queue, the quality of service (QoS) for the PU is guaranteed. Towards
Real-Time Collision Warning System Based on Computer Vision Using Mono Camera
This paper aims to help self-driving cars and autonomous vehicles systems to merge with the road environment safely and ensure the reliability of these systems in real life. Crash avoidance is a complex system that depends on many parameters. The forward-collision warning system is simplified into four main objectives: detecting cars, depth estimation, assigning cars into lanes (lane assign) and tracking technique. The presented work targets the software approach by using YOLO (You Only Look Once), which is a deep learning object detector network to detect cars with an accuracy of up to 93%
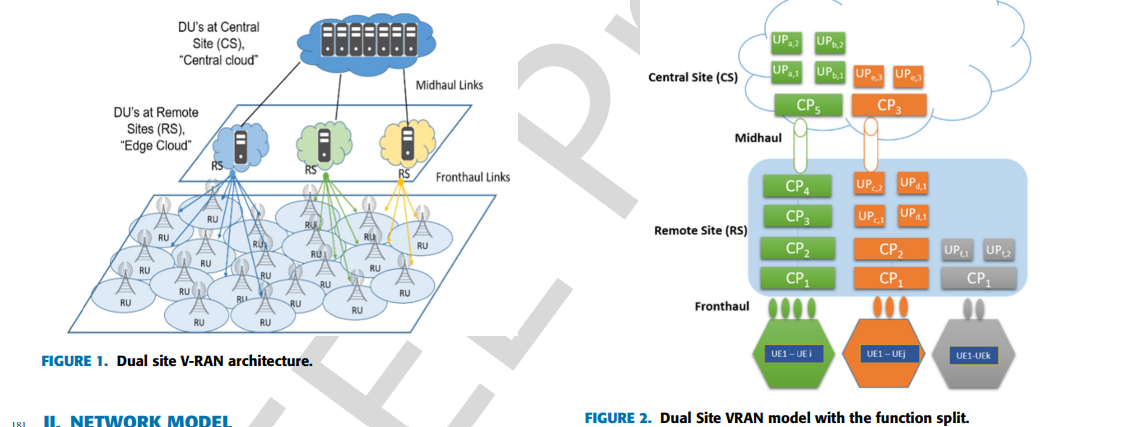
Optimum functional splits for optimizing energy consumption in V-RAn
A virtualized radio access network (V-RAN) is considered one of the key research points in the development of 5G and the interception of machine learning algorithms in the Telecom industry. Recent technological advancements in Network Function Virtualization (NFV) and Software Defined Radio (SDR) are the main blocks towards V-RAN that have enabled the virtualization of dual-site processing instead of all BBU processing as in the traditional RAN. As a result, several types of research discussed the trade-off between power and bandwidth consumption in V-RAN. Processing at remote locations

Interference alignment for secrecy
This paper studies the frequency/time selective K-user Gaussian interference channel with secrecy constraints. Two distinct models, namely the interference channel with confidential messages and the interference channel with an external eavesdropper, are analyzed. The key difference between the two models is the lack of channel state information (CSI) of the external eavesdropper. Using interference alignment along with secrecy precoding, it is shown that each user can achieve non-zero secure degrees of freedom (DoF) for both cases. More precisely, the proposed coding scheme achieves K-2/2K-2
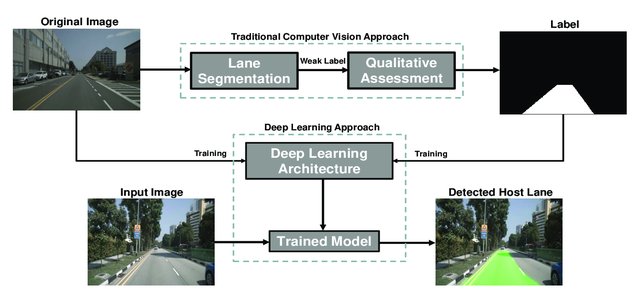
A Deep Learning-Based Benchmarking Framework for Lane Segmentation in the Complex and Dynamic Road Scenes
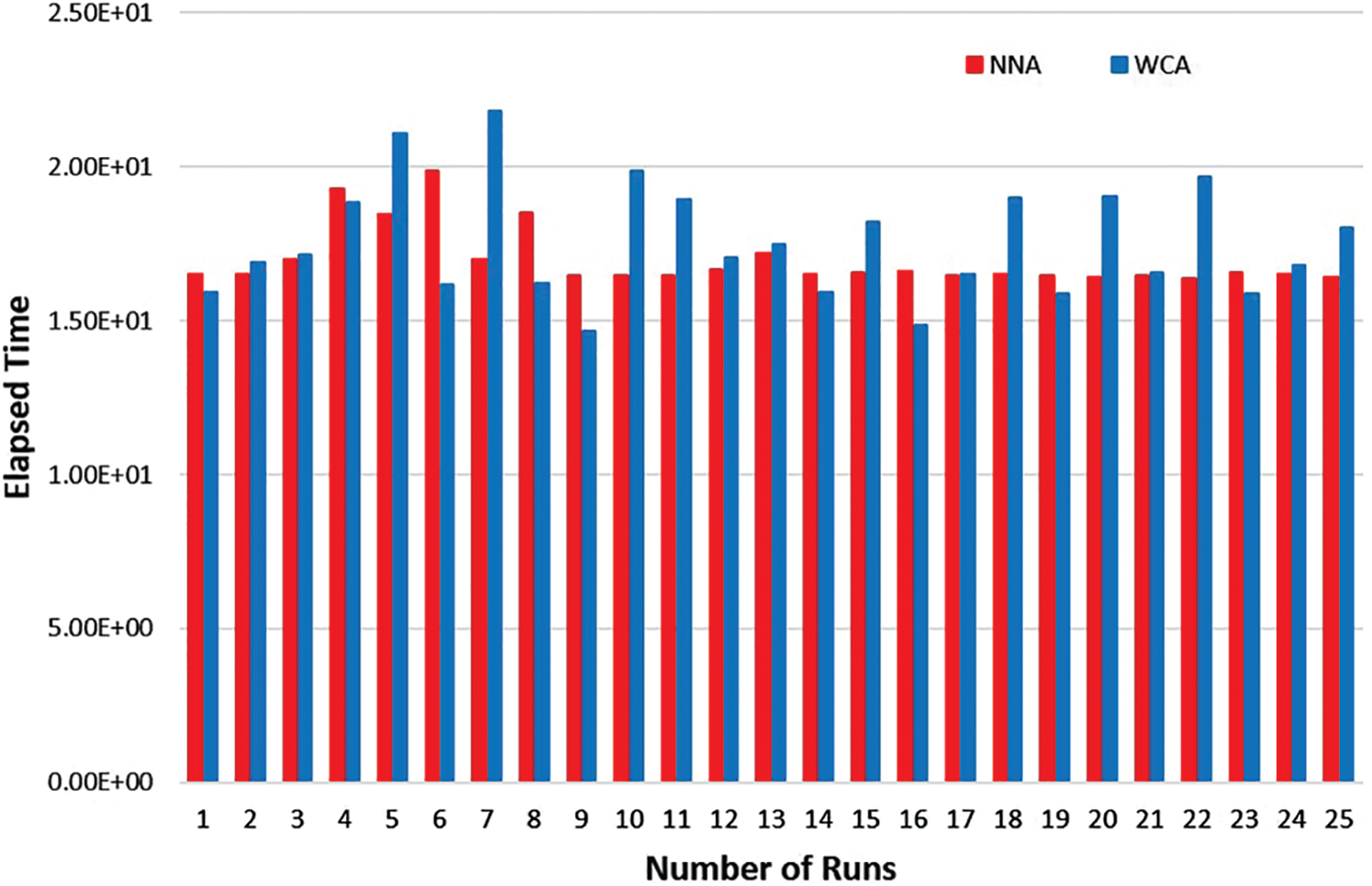
An artificial intelligence approach for solving stochastic transportation problems
Recent years witness a great deal of interest in artificial intelligence (AI) tools in the area of optimization. AI has developed a large number of tools to solve the most difficult search-and-optimization problems in computer science and operations research. Indeed, metaheuristic-based algorithms are a sub-field of AI. This study presents the use of the metaheuristic algorithm, that is, water cycle algorithm (WCA), in the transportation problem. A stochastic transportation problem is considered in which the parameters supply and demand are considered as random variables that follow the
Graph transformer for communities detection in social networks
Graphs are used in various disciplines such as telecommunication, biological networks, as well as social networks. In large-scale networks, it is challenging to detect the communities by learning the distinct properties of the graph. As deep learning has made contributions in a variety of domains, we try to use deep learning techniques to mine the knowledge from large-scale graph networks. In this paper, we aim to provide a strategy for detecting communities using deep autoencoders and obtain generic neural attention to graphs. The advantages of neural attention are widely seen in the field of
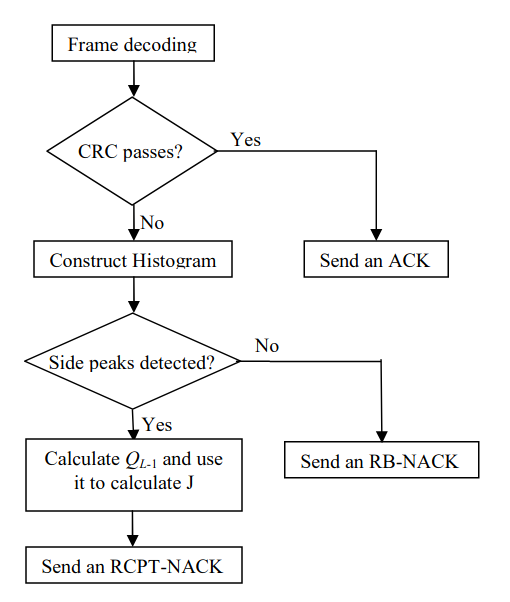
Novel reliability-based hybrid ARQ technique
In this paper we propose a novel technique for hybrid automatic repeat request (HARQ) systems where turbo codes are used as the forward error correction (FEC) techniques. This technique uses the histogram of the soft values generated by the turbo decoder to control the size and the contents of the retransmissions needed when the packet can not be decoded correctly. These soft values represent the reliabilities of the information bits; hence the proposed technique is a reliability-based (RB) HARQ technique. The proposed technique is compared to the conventional RB-HARQ and the conventional rate
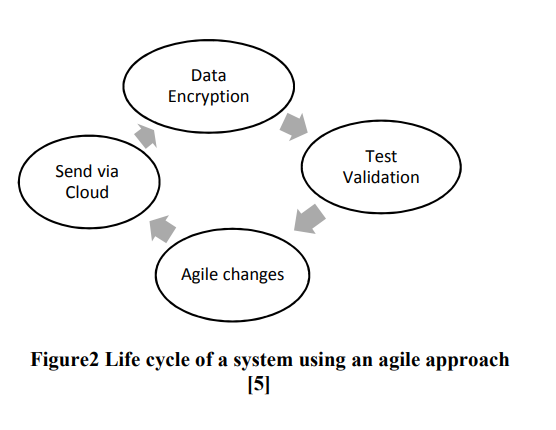
IoT Agile Framework Enhancement
Internet of Things (IoT) is considered as a trend nowadays. Devices connected to the internet interact with surrounding; this poses strong challenges in handling big data with a certain level of security. In this paper IoT devices will be divided in to two categories high vulnerability devices and low vulnerability devices. The classification depends on the ease of attacks. In order to ensure the security of IoT devices, an agile approach is used to secure high vulnerability devices as first step and then low vulnerability devices by applying encryption algorithms. © 2018 IEEE.

Transmit and receive cooperative cognition: Protocol design and stability analysis
In this paper, we investigate the stability of a cooperative cognitive system. We propose a cooperative secondary transmitter-receiver system (CSTR), where, the secondary transmitter (ST) and the secondary receiver (SR) increase the spectrum availability for the ST packets by relaying the unsuccessfully transmitted packets of the primary transmitter (PT). We assume receiving nodes with multipacket reception capability (MPR). We provide two inner bounds and two outer bounds on the stability region of the considered system. © 2013 ICST - The Institute for Computer Sciences, Social Informatics
Pagination
- Previous page ‹‹
- Page 7
- Next page ››
