Breadcrumb
Correction to: Optimization of energy-constrained wireless powered communication networks with heterogeneous nodes (Wireless Networks, (2019), 10.1007/s11276-017-1587-x)
The original version of this article contained error in author affiliation. Also, the article note and acknowledgement sections are missing. © 2018, Springer Science+Business Media, LLC, part of Springer Nature.
Comparative Analysis of Wind-loaded Telecom Tower Structures with Recommendations
Telecommunication towers are essential infrastructure in today's fast-paced world. Lattice self-supporting towers, monopole towers, and guyed towers are the three types of structures that can be used for telecommunications towers. When analyzing telecom tower loads, wind loads are the most important ones to address. As a result, it is necessary to choose an appropriate structure that can withstand the wind and the surrounding environment. The main aim of this paper is to propose a guideline for selecting the optimum tower structure based on the surrounding environment. In order to create this
Smart cloud platform for data management in the age of the internet of vehicles
Smart cars, with the emergence of the Internet of Vehicles (IoV), are expected to generate huge volumes of data at rates that typical data management systems will not be able to handle. Such data can be extremely useful to both analytics and machine learning applications. This paper discusses and demonstrates the process of architecting and building a scalable data management system for the IoV in a smart city environment, using Apache Spark, Apache Kafka and Apache Cassandra, which results in a scalable, resilient and fault-Tolerant data management system that facilitates performing big data
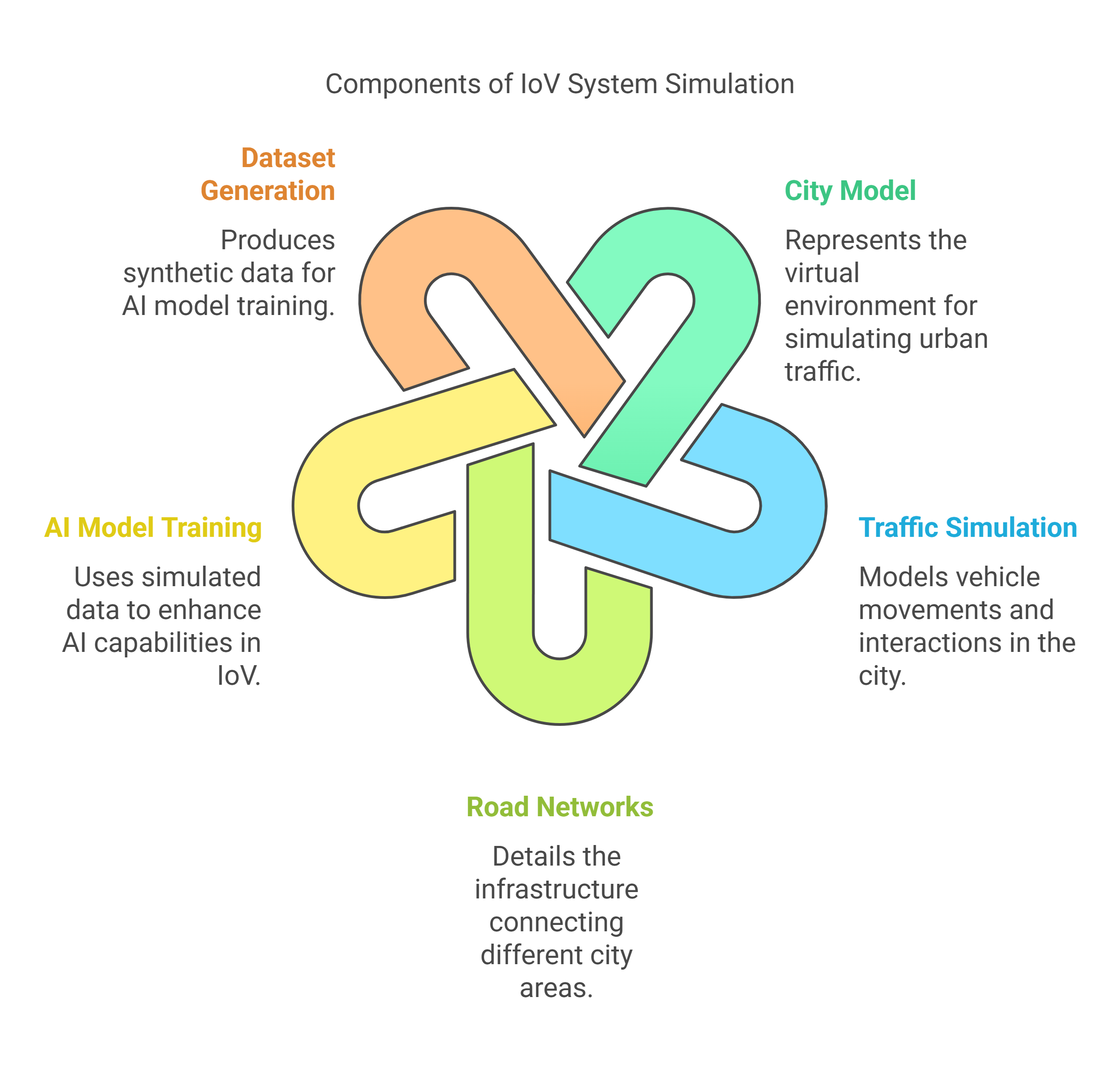
A Probabilistic City Model Generation for Application in Internet of Vehicles Technology
As the main pillar of the Smart City, Smart Highway manifests the centralized connectivity concept between the self-driving vehicles. Internet of Vehicle or IoV is the solution for improved connectivity between driverless vehicles. One of the major challenges in IoV research is the lack of datasets available. That is why the Internet of vehicles is one of the hot topics in research nowadays. IoV field is still a new topic in research, which leaves a huge shortage in the datasets available to train any Artificial Intelligent (AI) model for IoV systems. IoV systems have many research points such
Joint Content Valuations and Proactive Caching for Content Distribution Networks
Due to the advances in machine learning techniques, recommender systems nowadays are capable of learning and influencing the users' decisions. Hence, recommendations became an important facility to reduce the cost (or increase the profit) of the operators of the demand networks. In this paper we formulate and study the problem of dynamically optimizing the demand shaping, through content recommendation, and proactive caching. The formulated problem suffers from the curse of dimensionality, so we devise an approximate algorithm optimizing only over a short look-ahead window. The approximate
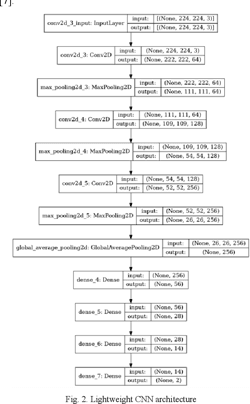
Light-Weight Food/Non-Food Classifier for Real-Time Applications
Today, automatic food/non-food classification became extremely important for many real-time applications, specifically since the pandemic of the COVID-19 virus. Such that the 'no food policy' now became applied more than ever to help decrease the spread of the COVID-19 virus. Consequently, many studies used deep neural networks for the food/non-food classification task, yet these deep neural networks were computationally expensive. As a result, in this paper, a lightweight Convolution Neural Network (CNN) is proposed and put into use for classifying foods and non-foods. Compared to prior
Secure Data Aggregation in Cultural Heritage Monitoring: NMEC Case Study
Intelligent management plays a vital role in the preservation and success of cultural heritage, particularly in the context of museums. To ensure the long-term safeguarding of valuable and significant artifacts housed in museums, regular inspections are necessary. In this specific research study, the National Museum of Egyptian Civilization (NMEC) serves as a case study. To effectively monitor the museum's environment and protect its cultural assets, a wireless sensor network (WSN) is proposed. This network comprises various sensors that monitor crucial environmental factors such as
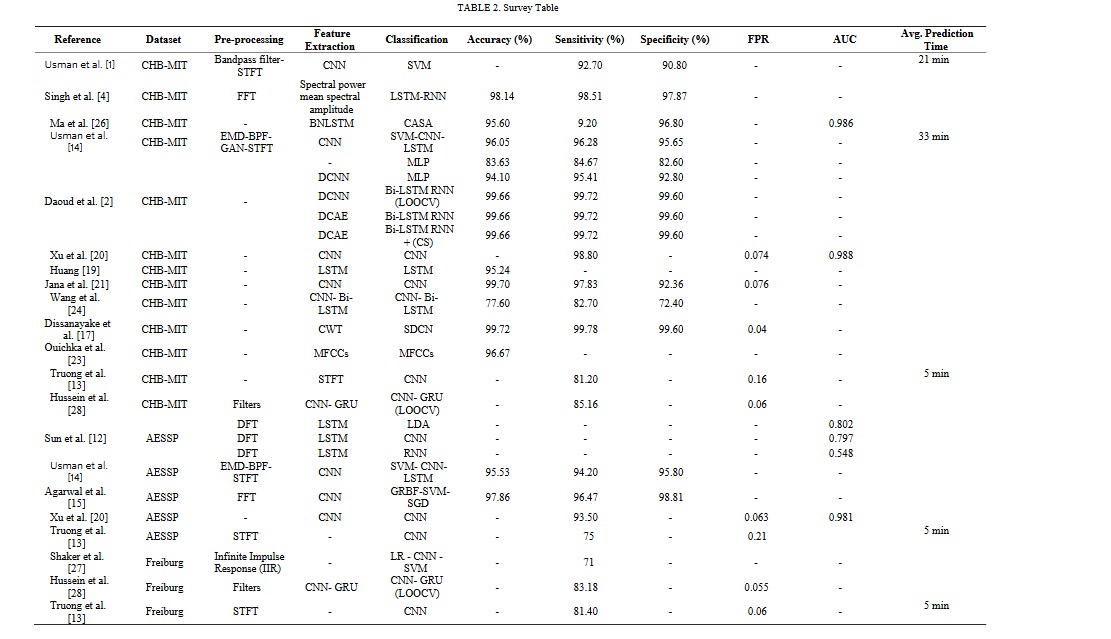
Deep Learning Approaches for Epileptic Seizure Prediction: A Review
Epilepsy is a chronic nervous disorder, which disturbs the normal daily routine of an epileptic patient due to sudden seizure onset that may cause loss of consciousness. Seizures are periods of aberrant brain activity patterns. Early prediction of an epileptic seizure is critical for those who suffer from it as it will give them time to prepare for an incoming seizure and alert anyone in their close circle of contacts to aid them. This has been an active field of study, powered by the decreasing cost of non-invasive electroencephalogram (EEG) collecting equipment and the rapid evolution of
Deep Learning-Based Context-Aware Video Content Analysis on IoT Devices
Integrating machine learning with the Internet of Things (IoT) enables many useful applica-tions. For IoT applications that incorporate video content analysis (VCA), deep learning models are usually used due to their capacity to encode the high-dimensional spatial and temporal representations of videos. However, limited energy and computation resources present a major challenge. Video captioning is one type of VCA that describes a video with a sentence or a set of sentences. This work proposes an IoT-based deep learning-based framework for video captioning that can (1) Mine large open-domain
Light-Weight Food Image Classification For Egyptian Cuisine
Food is an integral aspect of daily life in all cultures. It highly affects people's diets, eating behaviors, and overall health. People with poor eating habits are usually overweight or obese, which leads to chronic diseases such as diabetes and cardiovascular disease. Today, the classification of food images has several uses in managing medical conditions and dieting. Deep convolutional neural network (DCNN) architectures provide the foundation for the most recent food recognition models. However, DCNNs are computationally expensive due to high computation time and memory requirements. In
Pagination
- Previous page ‹‹
- Page 2
- Next page ››
