Breadcrumb
AROMA: Automatic generation of radio maps for localization systems
Current methods for building radio maps for wireless localization systems require a tedious, manual and error-prone calibration of the area of interest. Each time the layout of the environment is changed or different hardware is used, the whole process of location fingerprinting and constructing the radio map has to be repeated. The process gets more complicated in the case of localizing multiple entities in a device-free scenario, since the radio map needs to take all possible combinations of the location of the entities into account. In this demo, we present a novel system (AROMA) that is
Transmission power adaptation for cognitive radios
In cognitive radio (CR) networks, determining the optimal transmission power for the secondary users (SU) is crucial to achieving the goal of maximizing the secondary throughput while protecting the primary users (PU) from service disruption and interference. In this paper, we propose an adaptive transmission power scheme for cognitive terminals opportunistically accessing a primary channel. The PU operates over the channel in an unslotted manner switching activity at random times. The secondary transmitter (STx) adapts its transmission power according to its belief regarding the PU's state of
Hierarchical proactive caching for vehicular ad hoc networks
Recently, emerging vehicular applications are increasing the demand of vehicles which form significant burdens on network backhaul and represents a cause to the quality of experience (QoE) decay of the vehicular users. Proactive caching is a promising technique to mitigate the load on core networks by caching some of the expected data items. This work proposes a hierarchical proactive caching scheme which jointly considers caching in vehicles and roadside units (RSUs). Minimization of the vehicle communication latency is the main objective of our study. The optimization problem is formulated
Towards evolving sensor actor networks
Sensor Actor NETworks (SANET) represent a major component of ubiquitous service environments promising interesting solutions to a wide range of problems. Despite the obvious increase in the research activities proposing architectures and protocols for SANETs, we are still no where near the production of industrial-grade SANET software that can be relied upon for mission critical applications. The cost of programming, deploying and maintaining SANET environments is still highly prohibitive due to the lack of industrial tools capable of realizing adaptive SANET software in a cost effective way

Multi-reader RFID tag identification using bit tracking (MRTI-BT)
In this paper we study the problem of tag identification in multi-reader RFID systems. In particular, we propose a novel solution to the reader-to-reader collisions and tag collisions in multi-reader systems, using the concept of bit tracking [1]. Towards this objective, we propose the multi-reader RFID tag identification using bit tracking (MRTI-BT) algorithm which allows concurrent tag identification, by neighboring RFID readers, as opposed to time-consuming scheduling. First, MRTI-BT identifies tags exclusive to different RFIDs, concurrently. Second, the concept of bit tracking and the
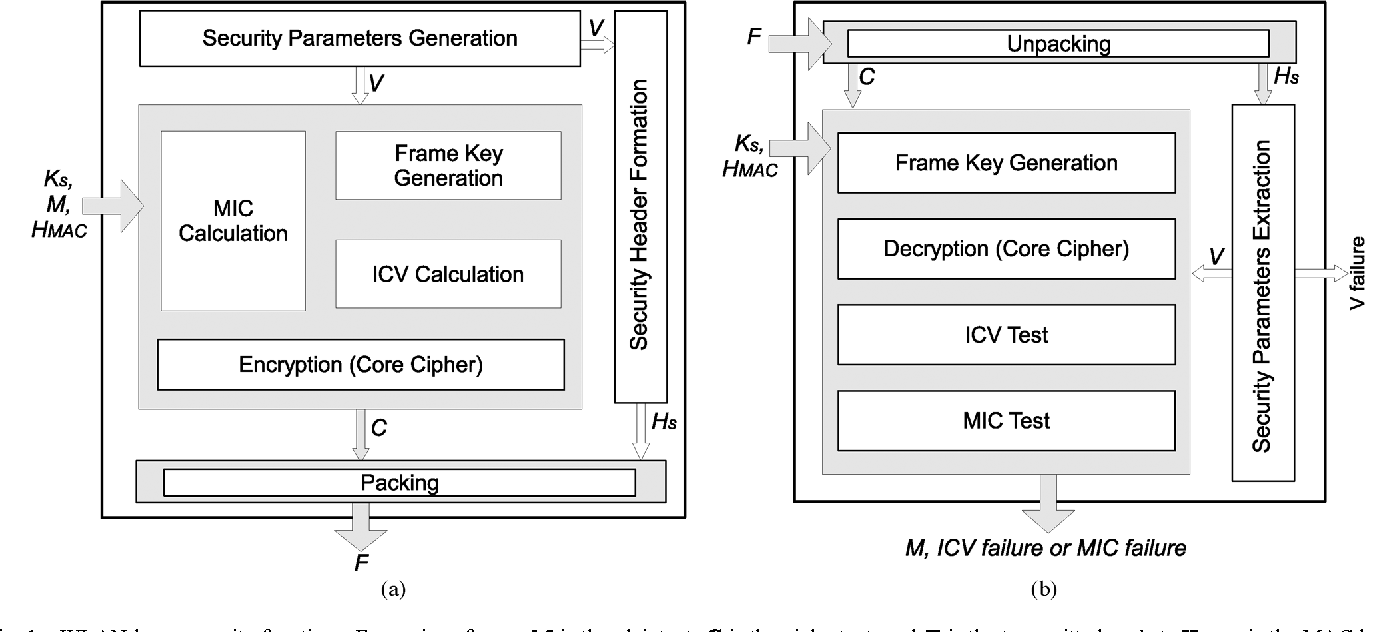
Keys through ARQ: Theory and practice
This paper develops a novel framework for sharing secret keys using the Automatic Repeat reQuest (ARQ) protocol. We first characterize the underlying information theoretic limits, under different assumptions on the channel spatial and temporal correlation function. Our analysis reveals a novel role of dumb antennas in overcoming the negative impact of spatial correlation on the achievable secrecy rates. We further develop an adaptive rate allocation policy, which achieves higher secrecy rates in temporally correlated channels, and explicit constructions for ARQ secrecy coding that enjoy low
Improved spectrum mobility using virtual reservation in collaborative cognitive radio networks
Cognitive radio technology would enable a set of secondary users (SU) to opportunistically use the spectrum licensed to a primary user (PU). On the appearance of this PU on a specific frequency band, any SU occupying this band should free it for PUs. Typically, SUs may collaborate to reduce the impact of cognitive users on the primary network and to improve the performance of the SUs. In this paper, we propose and analyze the performance of virtual reservation in collaborative cognitive networks. Virtual reservation is a novel link maintenance strategy that aims to maximize the throughput of
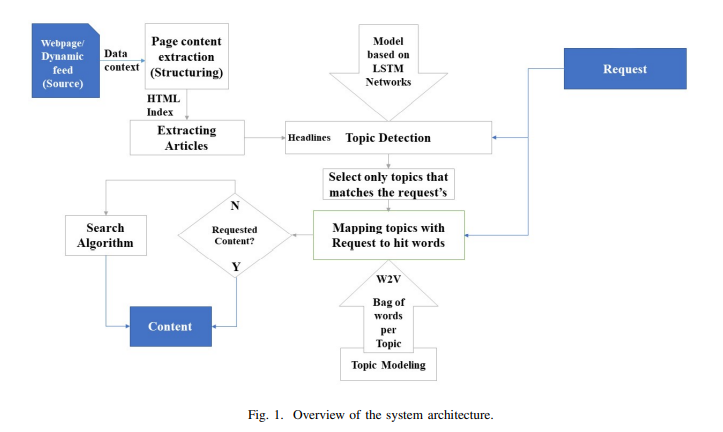
Towards Intelligent Web Context-Based Content On-Demand Extraction Using Deep Learning
Information extraction and reasoning from massive high-dimensional data at dynamic contexts, is very demanding and yet is very hard to obtain in real-time basis. However, such process capability and efficiency might be affected and limited by the available computational resources and the consequent power consumption. Conventional search mechanisms are often incapable of real-time fetching a predefined content from data source, without concerning the increased number of connected devices that contribute to the same source. In this work, we propose and present a concept for an efficient approach

Chaos-Based RNG using Semiconductor Lasers with Parameters Variation Tolerance
Random numbers play an essential role in guaranteeing secrecy in most cryptographic systems. A chaotic optical signal is exploited to achieve high-speed random numbers. It could be generated by using one or more semiconductor lasers with external optical feedback. However, this system faces two major issues, high peak to average power ratio (PAPR) and parameter variations. These issues highly affected the randomness of the generated bitstreams. In this paper, we use a non-linear compression technique to compand the generated signal before it is quantized to avoid the effects of the PAPR. Also
Reliability and Security Analysis of an Entanglement-Based QKD Protocol in a Dynamic Ground-to-UAV FSO Communications System
Quantum cryptography is a promising technology that achieves unconditional security, which is essential to a wide range of sensitive applications. In contrast to optical fiber, the free-space optical (FSO) link is efficiently used as a quantum channel without affecting the polarization of transmitted photons. However, the FSO link has several impairments, such as atmospheric turbulence and pointing errors, which affect the performance of the quantum channel. This paper proposes a quantum key distribution (QKD) scheme that uses a time-bin entanglement protocol over the FSO channel that suffers
Pagination
- Previous page ‹‹
- Page 8
- Next page ››
