Breadcrumb
A multiobjective nonlinear combinatorial model for improved planning of tour visits using a novel binary gaining-sharing knowledge- based optimization algorithm
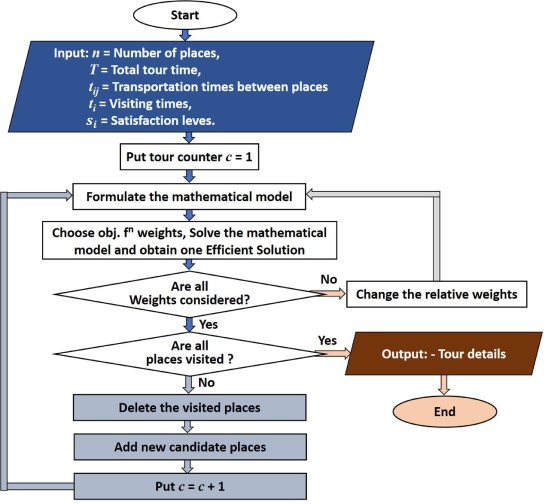
This chapter proposes a novel binary version of recently developed Gaining-Sharing knowledge-based optimization algorithm (GSK) to solve binary optimization problems. GSK algorithm is based on the concept of how humans acquire and share knowledge during their life span. Binary version of GSK named novel binary Gaining-Sharing knowledge-based optimization algorithm (BGSK) depends on mainly two binary stages: binary junior gaining sharing stage and binary senior gaining sharing stage with knowledge factor 1. These two stages enable BGSK for exploring and exploitation of the search space
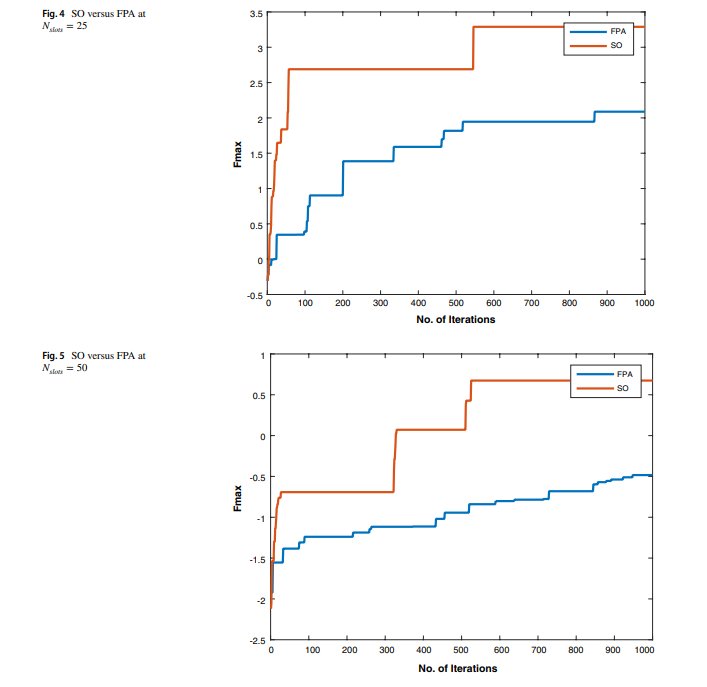
A power-aware task scheduler for energy harvesting-based wearable biomedical systems using snake optimizer
There is an increasing interest in energy harvesting for wearable biomedical devices. This requires power conservation and management to ensure long-term and steady operation. Hence, task scheduling algorithms will be used throughout this work to provide a reliable solution to minimize energy consumption while considering the system operation constraints. This study proposes a novel power-aware task scheduler to manage system operations. For example, we used the scheduler to handle system operations, including heart rate and temperature sensors. Two optimization techniques have been used to

Downlink Throughput Prediction in LTE Cellular Networks Using Time Series Forecasting
Long-Term Evolution (LTE) cellular networks have transformed the mobile business, as users increasingly require various network services such as video streaming, online gaming, and video conferencing. A network planning approach is required for network services to meet user expectations and meet their needs. The User DownLink (UE DL) throughput is considered the most effective Key Performance Indicator (KPI) for measuring the user experience. As a result, the forecast of UE DL throughput is essential in network dimensioning for the network planning team throughout the network design stage. The
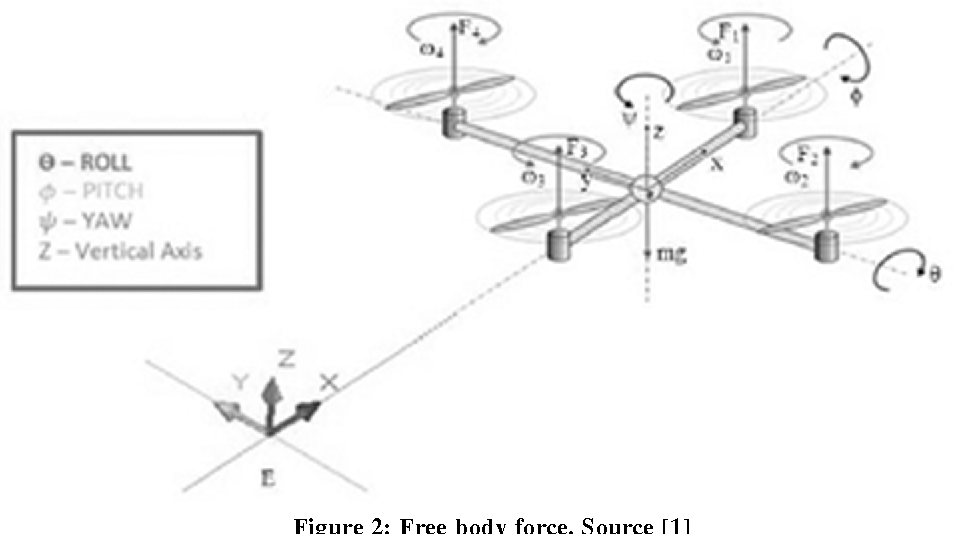
Self Balancing Quad-Copter Using PID Controller
Unmanned Aerial Vehicle (UAV) technology is considered one of the important technologies at present, which is believed to solve many problems in the future, such as delivering small-weighted goods, agriculture, and civil fields. This research paper presents the mathematical model of a quadcopter that was developed as an example of an unmanned aerial vehicle. The MATLAB and Simulink environment create the model simulation and controller design. The present study proposes a cost-effective and easily deployable control system with a comparison that shows the difference between the controller made
Implementation of Multi-Step Bias-Flip Rectifier for Piezoelectric Energy Harvesting
The full-wave rectifier is an essential step for extracting energy from a piezoelectric source. Yet, the inherent capacitance of the piezoelement significantly is considered a limitation of the efficiency of extraction. To address this issue, the bias-flip rectifier can be used. However, this rectifier needs large inductor and precise tuning. The large inductor increases the overall volume of the system which is inefficient. This paper address the problems with the traditional bias-flip rectifier by introducing an enhanced multi-step bias-flip rectifier to achieve a high voltage-flip
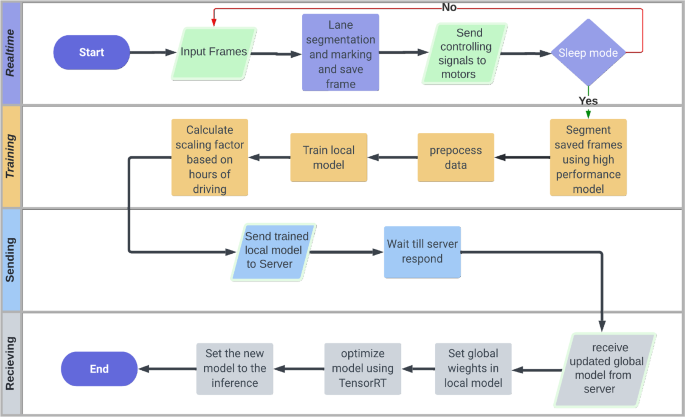
Federated learning system on autonomous vehicles for lane segmentation
Autonomous Vehicles (AV) is one of the most evolving industries in the last decade. However, one of the bottlenecks of this evolution is providing data that contains different scenarios and scenes to improve the models without exposing the privacy and security of the edge vehicles. The authors of this research propose a secure and efficient novel solution for lane segmentation in AVs through the use of Federated Learning (FL). FedLane involves initial training of U-Net, ResUNet, and ResUNet++ models, followed by real-time inference in edge devices and the application of FL to update the server
Light-Weight Face Shape Classifier for Real-Time Applications
Deep neural networks (DNNs) are memory and computationally intensive; hence they are difficult to apply to real-time systems with limited resources. Therefore, the DNN models need to be carefully optimized. The solution was a model based on a convolutional neural network (CNN) called MobileNet that decreases the computational and space complexities with classification precision loss by utilizing depthwise separable convolutions. This study uses MobileNet vl architecture to improve image classification complexities to reach an acceptable complexity that can be used in real-time applications
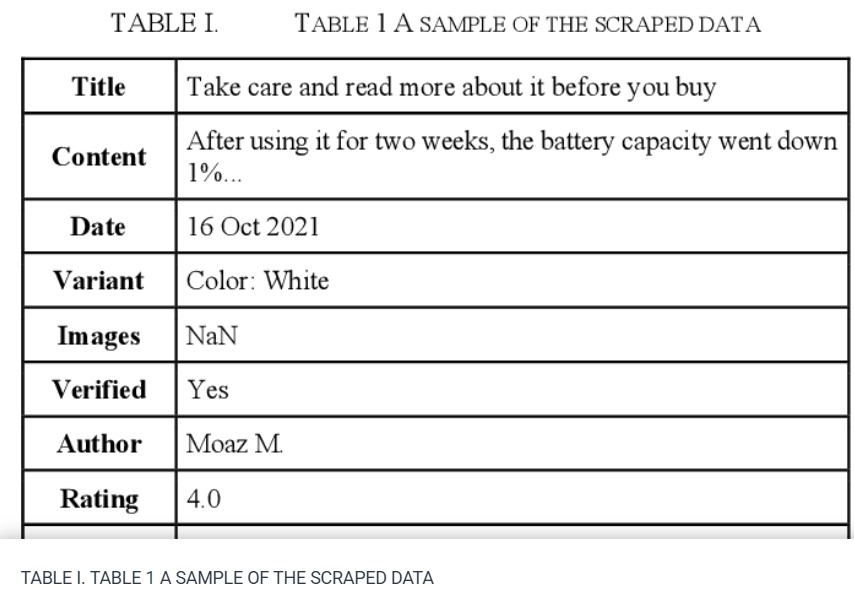
Sentiment Analysis: Amazon Electronics Reviews Using BERT and Textblob
The market needs a deeper and more comprehensive grasp of its insight, where the analytics world and methodologies such as 'Sentiment Analysis' come in. These methods can assist people especially 'business owners' in gaining live insights into their businesses and determining wheatear customers are satisfied or not. This paper plans to provide indicators by gathering real world Amazon reviews from Egyptian customers. By applying both Bidirectional Encoder Representations from Transformers 'Bert' and 'Text Blob' sentiment analysis methods. The processes shall determine the overall satisfaction
A Generic AI-Based Technique for Assessing Student Performance in Conducting Online Virtual and Remote Controlled Laboratories
Due to the COVID-19 pandemic and the development of educational technology, e-learning has become essential in the educational process. However, the adoption of e-learning in sectors such as engineering, science, and technology faces a particular challenge as it needs a special Laboratory Learning Management System (LLMS) capable of supporting online lab activities through virtual and controlled remote labs. One of the most challenging tasks in designing such LLMS is how to assess a student's performance while an experiment is being conducted and how stuttering students can be automatically
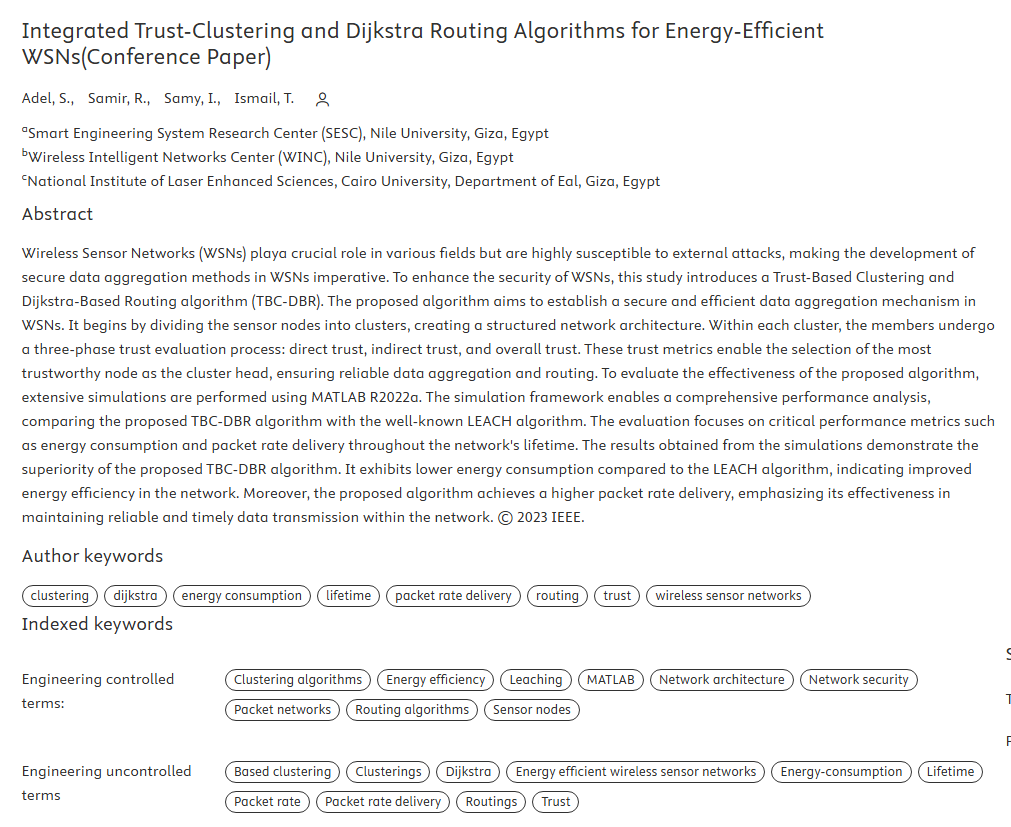
Integrated Trust-Clustering and Dijkstra Routing Algorithms for Energy-Efficient WSNs
Wireless Sensor Networks (WSNs) playa crucial role in various fields but are highly susceptible to external attacks, making the development of secure data aggregation methods in WSNs imperative. To enhance the security of WSNs, this study introduces a Trust-Based Clustering and Dijkstra-Based Routing algorithm (TBC-DBR). The proposed algorithm aims to establish a secure and efficient data aggregation mechanism in WSNs. It begins by dividing the sensor nodes into clusters, creating a structured network architecture. Within each cluster, the members undergo a three-phase trust evaluation process
Pagination
- Previous page ‹‹
- Page 4
- Next page ››
