Breadcrumb
Light-Weight Face Shape Classifier for Real-Time Applications
Deep neural networks (DNNs) are memory and computationally intensive; hence they are difficult to apply to real-time systems with limited resources. Therefore, the DNN models need to be carefully optimized. The solution was a model based on a convolutional neural network (CNN) called MobileNet that decreases the computational and space complexities with classification precision loss by utilizing depthwise separable convolutions. This study uses MobileNet vl architecture to improve image classification complexities to reach an acceptable complexity that can be used in real-time applications
Comparative Analysis of Wind-loaded Telecom Tower Structures with Recommendations
Telecommunication towers are essential infrastructure in today's fast-paced world. Lattice self-supporting towers, monopole towers, and guyed towers are the three types of structures that can be used for telecommunications towers. When analyzing telecom tower loads, wind loads are the most important ones to address. As a result, it is necessary to choose an appropriate structure that can withstand the wind and the surrounding environment. The main aim of this paper is to propose a guideline for selecting the optimum tower structure based on the surrounding environment. In order to create this
Integrated Trust-Clustering and Dijkstra Routing Algorithms for Energy-Efficient WSNs
Wireless Sensor Networks (WSNs) playa crucial role in various fields but are highly susceptible to external attacks, making the development of secure data aggregation methods in WSNs imperative. To enhance the security of WSNs, this study introduces a Trust-Based Clustering and Dijkstra-Based Routing algorithm (TBC-DBR). The proposed algorithm aims to establish a secure and efficient data aggregation mechanism in WSNs. It begins by dividing the sensor nodes into clusters, creating a structured network architecture. Within each cluster, the members undergo a three-phase trust evaluation process
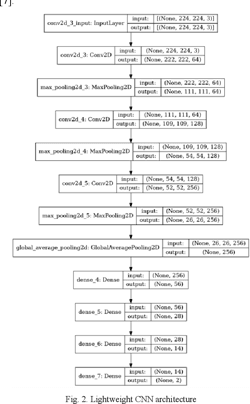
Light-Weight Food/Non-Food Classifier for Real-Time Applications
Today, automatic food/non-food classification became extremely important for many real-time applications, specifically since the pandemic of the COVID-19 virus. Such that the 'no food policy' now became applied more than ever to help decrease the spread of the COVID-19 virus. Consequently, many studies used deep neural networks for the food/non-food classification task, yet these deep neural networks were computationally expensive. As a result, in this paper, a lightweight Convolution Neural Network (CNN) is proposed and put into use for classifying foods and non-foods. Compared to prior

In the Identification of Arabic Dialects: A Loss Function Ensemble Learning Based-Approach
The automation of a system to accurately identify Arabic dialects many natural language processing tasks, including sentiment analysis, medical chatbots, Arabic speech recognition, machine translation, etc., will greatly benefit because it’s useful to understand the text’s dialect before performing different tasks to it. Different Arabic-speaking nations have adopted various dialects and writing systems. Most of the Arab countries understand modern standard Arabic (MSA), which is the native language of all other Arabic dialects. In this paper we propose a method for identifying Arabic dialects

Stability Analysis and Fault Detection of Telecommunication Towers Using Decision Tree Algorithm under Wind Speed Condition
This paper presents a decision tree (DT) modeling technique to estimate any increase in the load on telecommunication towers. A structural analysis was done for the lattice and mono-pole towers using TNX Tower software to determine the basic features of the towers, such as tilt angle, deflection, twist, and acceleration. The structure analysis generated a data set based on wind speeds. This data set was then used to train a machine-learning algorithm to estimate the loads on the structure. Any change in the applied loads greater than the loads considered in the design might be identified using
Optimum Selection of Communication Tower Structures Based on Wind Loads & lifecycle cost analysis
Communication towers are vital assets in our daily lives as they transfer signals between cell phones facilitating communication and commerce among people and businesses all around the world. Wind loads are crucial in the communication towers design since they are tall and slender. With climate change bringing more storms and higher wind speeds, it is more crucial to research the finest tower structure that withstands such conditions with the least life cycle cost. Therefore, in this paper, a comparative case study is performed between 45 m height lattice tower and monopole tower in Egypt. Two
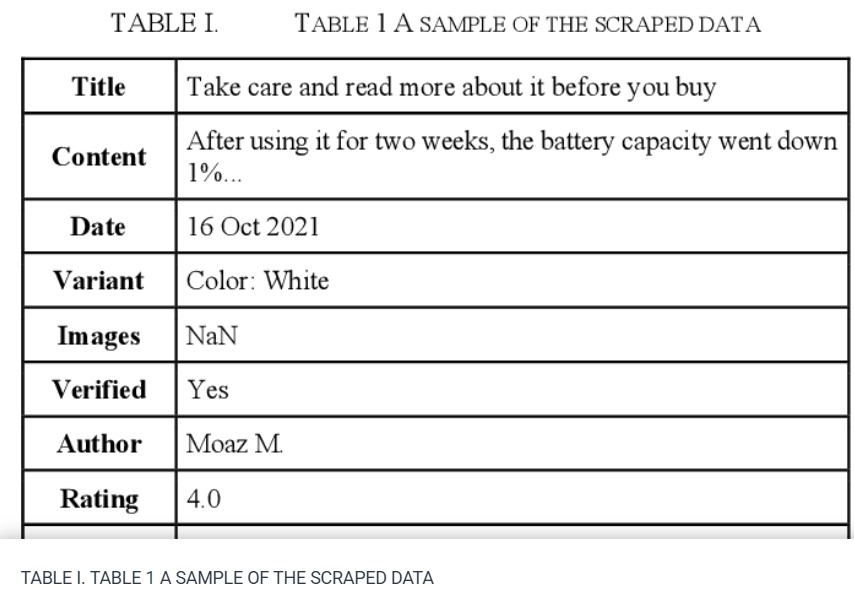
Sentiment Analysis: Amazon Electronics Reviews Using BERT and Textblob
The market needs a deeper and more comprehensive grasp of its insight, where the analytics world and methodologies such as 'Sentiment Analysis' come in. These methods can assist people especially 'business owners' in gaining live insights into their businesses and determining wheatear customers are satisfied or not. This paper plans to provide indicators by gathering real world Amazon reviews from Egyptian customers. By applying both Bidirectional Encoder Representations from Transformers 'Bert' and 'Text Blob' sentiment analysis methods. The processes shall determine the overall satisfaction
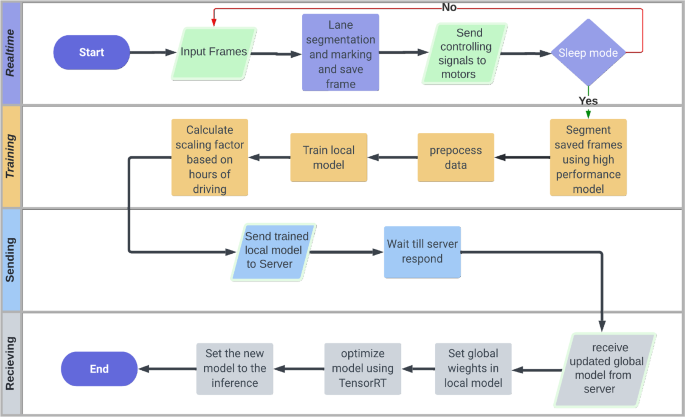
Federated learning system on autonomous vehicles for lane segmentation
Autonomous Vehicles (AV) is one of the most evolving industries in the last decade. However, one of the bottlenecks of this evolution is providing data that contains different scenarios and scenes to improve the models without exposing the privacy and security of the edge vehicles. The authors of this research propose a secure and efficient novel solution for lane segmentation in AVs through the use of Federated Learning (FL). FedLane involves initial training of U-Net, ResUNet, and ResUNet++ models, followed by real-time inference in edge devices and the application of FL to update the server
Light-Weight Food Image Classification For Egyptian Cuisine
Food is an integral aspect of daily life in all cultures. It highly affects people's diets, eating behaviors, and overall health. People with poor eating habits are usually overweight or obese, which leads to chronic diseases such as diabetes and cardiovascular disease. Today, the classification of food images has several uses in managing medical conditions and dieting. Deep convolutional neural network (DCNN) architectures provide the foundation for the most recent food recognition models. However, DCNNs are computationally expensive due to high computation time and memory requirements. In
Pagination
- Previous page ‹‹
- Page 2
- Next page ››
